|
SEC - Simple Event Correlation
- (updated 2007-07-29)
|
Protection against... |
Detection... |
Ease to install |
User usage
(green=easy) |
| |
funds transfert |
simple phishing |
MITM phishing |
ISP pharming |
trojan keylogger |
advanced trojan |
before-fraud |
after-fraud |
| |
|
N/A |
N/A |
N/A |
N/A |
N/A |
By Corp |
N/A |
|
|
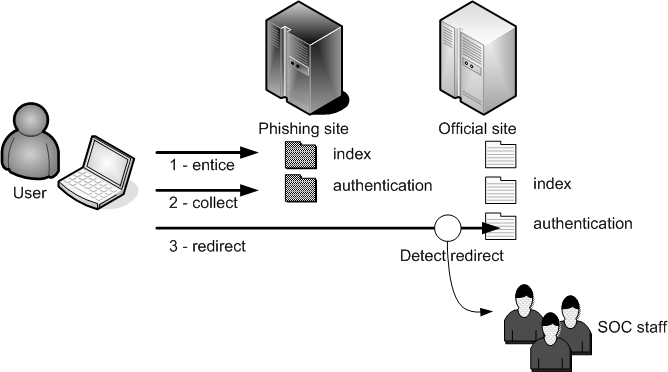
Goal : helping SOC or back-office staff to identify fraud
Installed by : back office service or business lines
In this scenario, we'll use the ability to make a real usage of HTTP
referer. Since some phishing sites only redirects users when data have
been collected or they download data (images) directly on the real
site, it's possible to collect the referer field and analyze it. If the
referer begins with our website name, it's ok, but if the referer is
something unexpected, then that probably mean that a phishing site is
using a complete or partial man in the middle fraud.
To enforce this, we'll use SEC ( http://www.estpak.ee/~risto/sec/).
The following SEC rule file will detect when an access has been done on
the authentication verification page and with a referer different from
the real site.
Rule file
# Bad Referer
# -----------
#
type=single
ptype=regexp
desc=Bad referer for authentication page
# This pattern means we look at everything coming from a website
diffrent from ours when it links to the authentication URI and when the
server answer with a 200 (OK) status code. You need to change MYURL and
MYSITE
pattern=\[\S+\s+\S+\]\s+\>\s+(-|http\:\/\/(?!MYSITE)\S*))\s+\-\>\s+\S*MYURL\S*\s+\>\s+200
action=pipe '$0' /usr/bin/mailx -s "[PHISHING ALERT] $1" soc@mysite.com
Apache configuration
# This line has to be in your apache httpd.conf file or apache2.conf file
LogFormat "%t > %{Referer}i -> %U > %s" customreferer
# This lien has to be in your virtualhost file. This virtualhost is the
site used for authentication check
CustomLog /var/log/apache2/custom.log customreferer
SEC usage
Remember to follow your log file with sec (you may have to configure automated task such as logrotate)
sec -conf=/etc/sec/sec_rule -input=/var/log/apache2/custom.log
|
