DNSP - Domain Name System Protection - (updated 2007-07-29)
|
Protection against... |
Detection... |
Ease to install |
User usage
(green=easy) |
| |
funds transfert |
simple phishing |
MITM phishing |
ISP pharming |
trojan keylogger |
advanced trojan |
before-fraud |
after-fraud |
| |
|
|
|
|
N/A |
N/A |
N/A |
N/A |
|
Corp |
Home |
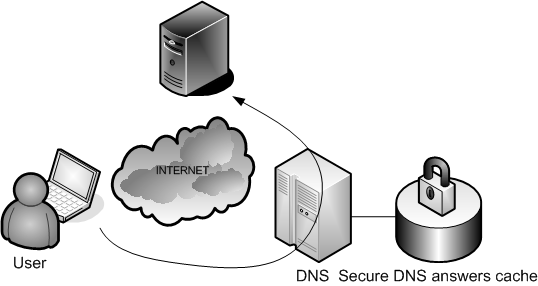
Goal : protecting user through sanitized resolving.
Installed by : IT/Network service
There, we will use a DNS server specially built to prevent phishing and
pharming attack. Thus, no answer are transmitted when the server
is asked addresses that are known phishing sites.
We will have all our requests forwarded to "opendns.com" —
which is a free open DNS server protected against pharming attacks
— and use the Netcraft database to identify phishing requests.
A user can also (on his own) decide to use the "opendns.com" server instead of the DNS server of his own ISP. It may help him preventing
from being redirected to a phishing site. However, having home users
changing their network configuration only happens once in a blue moon,
since most of the time, they entirely rely on DHCP to do as much
automation as possible!
Nevertheless, this solution
is mainly focused on protecting against phishing inside a company, so it's quite limited.
Furthermore, a new phishing site may be available on the Internet, but not be identified as one, yet.
DNS Configuration for bind 9 when configured in a caching server
acl allowed-internal-dns-servers {
192.168.15.0/24;
}
options {
directory "/var/named";
version "unknown version ";
allow-query{ allowed-internal-dns-servers; };
forwarders {
// Following addresses are those given by opendsn.com
// One should also add its own ISP DNS addresses to protect against opendsn.com unavailability
208.67.222.222;
208.67.220.220
};
forward only;
};
It is also
possible to subscribe to the Netcraft phishing site feed. This way, and
with some crafted scripts, you'll directly receive the list of newly
detected phishing Web sites identified by the Netcraft community. This
can be a way to build a custom and phishing protection-oriented DNS
cache.
